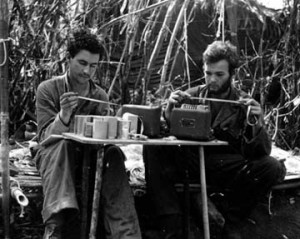
Merrill’s Marauders Message Center in Burma. Photo courtesy of Merrill’s Marauders Association. Used with permission.
The annual Military Radio Collectors Group meeting at Camp San Luis Obispo is almost here! This year, I’m pleased to announce that we’ll be conducting a joint crypto-related operation with the Maritime Radio Historical Society’s Coast Station KSM. Here’s their announcement of the operation.
As a commercially-licensed station, KSM is not bound by the restrictions on use of cryptography that ham radio operators are. They’ll be transmitting two different messages, both enciphered with a WW-2 era M-209 Converter. MRCG participants will, in turn, attempt to receive those messages and decipher them.
From the MRHS announcement, here’s the broadcast schedule:
KSM will broadcast a prepared message consisting of 26 groups encrypted with the M-209 at 15wpm on all its CW frequencies beginning at 1100 Pacific time (1800Z) on Saturday 4 May.
These frequencies are (in kc):
426 (after an announcement on 500)
4350.5
6474.0
8438.3
12993.0
16914.0
22445.8
The message will be sent twice.
The usual KSM press transmission will begin at 1000 Pacific time (1700Z) at 25wpm and continue until the announcement for the crypto broadcast to give listeners a chance to tune to the strongest signal in their area.
Upon completion of the CW transmissions a longer message will be sent on all KSM RTTY frequencies, also encrypted with the M-209. These frequencies are (in kc):
6328.0
8433.0
12631.0
The RTTY transmission will be 170cps shift Baudot, 45 baud.
Both the CW and RTTY messages will be encrypted with the same M-209 key settings.
Anybody capable of receiving KSM’s transmissions is welcome to participate, too! If you don’t have access to a real M-209, then you can use this free Windows-based M-209 simulator, or any of the other M-209 simulators out there.
If you don’t know how to operate an M-209 yet, then you might like to read my series of posts on practical use of the M-209. It’s not yet complete, but the existing chapters cover the basics of operating the machine.
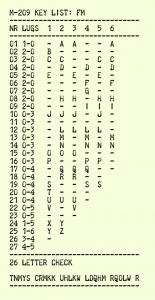
Finally, you will need the proper key in order to decipher the messages:
Received your KSM transmission Saturday morning, and decrypted using the m209 commandline tools. Thanks! Here is a video of my teletype model 19 receiving it: http://www.youtube.com/watch?v=paloUgyDJKo
Also copied it to punched tape: http://teletweety.com/m209-tape.jpg
That was fun!
Thank you very much for your reception report! I won’t be able to watch your video until I get back home from the MRCG meeting, but I and a few others I’ve told about it are looking forward to seeing it.
At the MRCG event in San Luis Obispo, CA, Tim Sammons N6CC and Tom Horsfall WA6OPE were able to copy the CW transmission despite fairly poor signal conditions. Tim had a single-character error that we corrected from Tom’s copy, and it wouldn’t have made the message difficult to understand anyway. The message indicator and its duplicate copy were intact. Hooray! The message, once deciphered, was an actual message received by Merrill’s Marauders during WW2 in Burma, deciphered on an M-209.
We were not able to copy the longer RTTY message at the event due to poor signal conditions, though. We used John Castorina WB6AZP’s AN/GRC-46 set for RTTY reception. The beginning and end of the message were lost in signal fades, so the intact portion was not usable without the message indicator. I am very happy to hear that at least one person received the RTTY transmission and managed to decipher it correctly! That message is a portion of another original message that Tim Sammons provided. I don’t recall its history, though.